BLOGs:
Blog-47:The Tech Trend:Beyond the Metrics: Why Current AI Security Is No Longer Enough
Artificial Intelligence (AI) has rapidly become one of the defining technologies of modern cybersecurity, deeply integrated into intrusion detection systems, malware analysis pipelines, fraud detection platforms, behavioral monitoring frameworks, and Security Operations Center (SOC) automation...Read PDF
Artificial Intelligence (AI) has rapidly become one of the defining technologies of modern cybersecurity, deeply integrated into intrusion detection systems, malware analysis pipelines, fraud detection platforms, behavioral monitoring frameworks, and Security Operations Center (SOC) automation...Read PDF
2026
Blog-46:The Tech Trend:AI Foundations to AI Frontiers in Cybersecurity: The Journey of BCCC Canada
Artificial Intelligence (AI) has rapidly transformed modern cybersecurity, enabling intelligent threat detection, malware analysis, behavioral monitoring, and automated defense mechanisms across complex digital environments. However, many early AI-driven cybersecurity systems were developed and evaluated under controlled laboratory conditions using limited datasets and simplified attack scenarios. While these systems, ...Read PDF
Artificial Intelligence (AI) has rapidly transformed modern cybersecurity, enabling intelligent threat detection, malware analysis, behavioral monitoring, and automated defense mechanisms across complex digital environments. However, many early AI-driven cybersecurity systems were developed and evaluated under controlled laboratory conditions using limited datasets and simplified attack scenarios. While these systems, ...Read PDF
2026
Blog-45:The Tech Trend:Understanding AI in Cybersecurity and AI Security: AI Safety and Fairness Nowadays Explained (UCSAISec-05)
As AI technologies advance at an unprecedented speed, their societal risks are becoming as visible as their benefits. Policymakers and researchers now rank AI safety concerns alongside global-scale threats, yet safeguards trail behind innovation. From biased recruitment tools and unfair credit scoring to wrongful arrests, the dangers are already present, while future misuse may extend to disinformation campaigns, cyberattacks, and even biotechnology. This Article, ...Read PDF
As AI technologies advance at an unprecedented speed, their societal risks are becoming as visible as their benefits. Policymakers and researchers now rank AI safety concerns alongside global-scale threats, yet safeguards trail behind innovation. From biased recruitment tools and unfair credit scoring to wrongful arrests, the dangers are already present, while future misuse may extend to disinformation campaigns, cyberattacks, and even biotechnology. This Article, ...Read PDF
2025
Blog-44:The Tech Trend:Understanding AI in Cybersecurity and AI Security: Defense Methods for Adversarial Attacks and Privacy Issues in Secure AI (UCSAISec-04)
As AI systems become more common in the real world, powering self-driving cars, medical tools, and surveillance, they’ve also become exposed to new kinds of threats. One serious threat is the adversarial attack, where small changes to input data mislead a model into making incorrect predictions. These changes are usually invisible to humans but can completely alter the model’s output. This Article, ...Read PDF
As AI systems become more common in the real world, powering self-driving cars, medical tools, and surveillance, they’ve also become exposed to new kinds of threats. One serious threat is the adversarial attack, where small changes to input data mislead a model into making incorrect predictions. These changes are usually invisible to humans but can completely alter the model’s output. This Article, ...Read PDF
2025
Blog-43:The Tech Trend:Understanding AI in Cybersecurity and AI Security: AI Security and Privacy (UCSAISec-03)
AI is revolutionizing every industry it touches, but its growing integration into critical systems also opens new security vulnerabilities. As machine learning models become more sophisticated, they attract attackers who aim to exploit their design, data, and functionality. This article, ...Read PDF
AI is revolutionizing every industry it touches, but its growing integration into critical systems also opens new security vulnerabilities. As machine learning models become more sophisticated, they attract attackers who aim to exploit their design, data, and functionality. This article, ...Read PDF
2025
Blog-42:The Tech Trend:Understanding AI in Cybersecurity and AI Security: AI in IoT and OT Security (UCSAISec-02)
The Internet of Things has fundamentally changed how we interact with technology, creating networks of smart devices that talk to each other and collect valuable data. Unlike traditional computers, IoT creates a blend between physical objects and digital capabilities, opening new possibilities for automation and interaction. This article, ...Read PDF
The Internet of Things has fundamentally changed how we interact with technology, creating networks of smart devices that talk to each other and collect valuable data. Unlike traditional computers, IoT creates a blend between physical objects and digital capabilities, opening new possibilities for automation and interaction. This article, ...Read PDF
2025
Blog-41:The Tech Trend: Understanding AI in Cybersecurity and AI Security:AI in Cybersecurity (UCSAISec-01)
Artificial intelligence (AI) is used in more tools to protect our data. With its ability to crunch vast volumes of data, recognize patterns, and adapt to new threats, AI helps cybersecurity shift from reactive to proactive. It’s not just about blocking known threats anymore – AI helps us spot suspicious behavior before something goes wrong. This article ...Read PDF
Artificial intelligence (AI) is used in more tools to protect our data. With its ability to crunch vast volumes of data, recognize patterns, and adapt to new threats, AI helps cybersecurity shift from reactive to proactive. It’s not just about blocking known threats anymore – AI helps us spot suspicious behavior before something goes wrong. This article ...Read PDF
2025
Blog-40: The Tech Trend: Understanding Cybersecurity management in Healthcare: Cybersecurity Cybersecurity Challenges, Best Practices, and Future Work in Healthcare (Article 4)
As healthcare professionals, IT professionals, and decision-makers in healthcare organizations, your role in exploring and addressing the potential security and privacy concerns in healthcare systems is crucial and highly valued. (Jawad, 2024)...Read PDF
As healthcare professionals, IT professionals, and decision-makers in healthcare organizations, your role in exploring and addressing the potential security and privacy concerns in healthcare systems is crucial and highly valued. (Jawad, 2024)...Read PDF
2024
Blog-39: The Tech Trend: Understanding Cybersecurity management in Healthcare: Cybersecurity Governance and Ethics in Healthcare (Article 3)
Data governance in healthcare sets the framework for decision-making and accountability around managing data – from its creation and use to its final archiving or disposal (Gartner, 2024). It’s crucial for making data in all forms available, secure, and useful across healthcare organizations...Read PDF
Data governance in healthcare sets the framework for decision-making and accountability around managing data – from its creation and use to its final archiving or disposal (Gartner, 2024). It’s crucial for making data in all forms available, secure, and useful across healthcare organizations...Read PDF
2024
Blog-38: The Tech Trend: Understanding Cybersecurity management in Healthcare: Detection and Prevention of Cyber-attacks in Healthcare (Article 2)
Cybersecurity is no longer just a technical issue for the IT department in healthcare – it’s a frontline defense for patient safety, operational continuity, and institutional trust. The healthcare industry faces unique challenges due to its reliance on sensitive data,...Read PDF
Cybersecurity is no longer just a technical issue for the IT department in healthcare – it’s a frontline defense for patient safety, operational continuity, and institutional trust. The healthcare industry faces unique challenges due to its reliance on sensitive data,...Read PDF
2024
Blog-37: The Tech Trend: Understanding Cybersecurity management in Healthcare: Defining Cybersecurity in Healthcare (Article 1)
With healthcare accounting for 34% of cyberattacks in 2023, the sector is a prime target for cybercriminals exploiting vulnerabilities. Cybersecurity is a critical lifeline for safeguarding sensitive patient data and ensuring medical systems operate without interruption...Read PDF
With healthcare accounting for 34% of cyberattacks in 2023, the sector is a prime target for cybercriminals exploiting vulnerabilities. Cybersecurity is a critical lifeline for safeguarding sensitive patient data and ensuring medical systems operate without interruption...Read PDF
2024
Blog-36: The Tech Trend: Understanding Cybersecurity on Smartphones (UCSph) - The Challenges in Mobile Application Security 2024 (Article 4)
As mobile apps become integral to our lives, they also expose users to a growing range of security threats. These threats exploit system vulnerabilities, impacting both individuals and connected systems...Read PDF
As mobile apps become integral to our lives, they also expose users to a growing range of security threats. These threats exploit system vulnerabilities, impacting both individuals and connected systems...Read PDF
2024
Blog-35: Cybers Guards: Understanding Cybersecurity on Smartphones (UCSph) - (Article 3)
Are you curious about niche smartphone OS options beyond Windows, Android, and iOS? This article explores seven alternative operating systems: Symbian, Tizen OS, Sailfish OS, Ubuntu Touch, KaiOS, Sirin OS, and Harmony OS. These players add spice to the mobile OS mix with unique offerings and approaches to security....Read PDF
Are you curious about niche smartphone OS options beyond Windows, Android, and iOS? This article explores seven alternative operating systems: Symbian, Tizen OS, Sailfish OS, Ubuntu Touch, KaiOS, Sirin OS, and Harmony OS. These players add spice to the mobile OS mix with unique offerings and approaches to security....Read PDF
2024
Blog-34: IT World Canada: Understanding Cybersecurity on Smartphones (UCSph) - Windows Phone Operating System (Article 2)
The Windows Phone was first known as Windows Mobile in its early days, until Microsoft recognized the need to adapt and innovate in response to the competitive landscape of the smartphone market. After the changes introduced by Apple (iOS) and Google (Android) in 2007, Microsoft decided to take a new direction and created Windows Phone as a response...Read PDF
The Windows Phone was first known as Windows Mobile in its early days, until Microsoft recognized the need to adapt and innovate in response to the competitive landscape of the smartphone market. After the changes introduced by Apple (iOS) and Google (Android) in 2007, Microsoft decided to take a new direction and created Windows Phone as a response...Read PDF
2024
Blog-33: IT World Canada: Understanding Cybersecurity on Smartphones (UCSph) - iOS Operating System (Article 1)
The smartphone is one of the most remarkable inventions in contemporary human history and is currently the most widely utilized electronic device globally. Its evolution has transformed modern communication technology, allowing us to communicate efficiently and instantly across vast distances worldwide...Read PDF
The smartphone is one of the most remarkable inventions in contemporary human history and is currently the most widely utilized electronic device globally. Its evolution has transformed modern communication technology, allowing us to communicate efficiently and instantly across vast distances worldwide...Read PDF
2024
Blog-32: IT World Canada: Understanding Cybersecurity Management in DeFi (UCM-DeFi) – Smart Contracts and DeFi Security and Threats (Article 5)
Smart contracts have transformed how legal agreements are managed and carried out, but they come with their own share of potential flaws and security risks. These shortcomings make smart contracts susceptible to hacking, which can lead to substantial financial losses...Read PDF
Smart contracts have transformed how legal agreements are managed and carried out, but they come with their own share of potential flaws and security risks. These shortcomings make smart contracts susceptible to hacking, which can lead to substantial financial losses...Read PDF
2023
Blog-31: IT World Canada: Understanding Cybersecurity Management in DeFi (UCM-DeFi) – Blockchain Security (Article 4)
In today’s digital landscape, blockchain technology has emerged as a powerful force, revolutionizing sectors like healthcare, finance, government, and commerce with its unparalleled security features. However, as with any technological advancement, it has not been immune to the cunning tactics of cybercriminals...Read PDF
In today’s digital landscape, blockchain technology has emerged as a powerful force, revolutionizing sectors like healthcare, finance, government, and commerce with its unparalleled security features. However, as with any technological advancement, it has not been immune to the cunning tactics of cybercriminals...Read PDF
2023
Blog-30: IT World Canada: Understanding Cybersecurity Management in DeFi (UCM-DeFi) – DeFi Platforms (Article 3)
With the help of blockchain and smart contracts, DeFi platforms are shaking up the financial industry by offering a wide range of services without the need for intermediaries like banks or brokerages. From lending and borrowing to trading and even gaming, DeFi is changing the way we access financial services...Read PDF
With the help of blockchain and smart contracts, DeFi platforms are shaking up the financial industry by offering a wide range of services without the need for intermediaries like banks or brokerages. From lending and borrowing to trading and even gaming, DeFi is changing the way we access financial services...Read PDF
2023
Blog-29: IT World Canada: Understanding Cybersecurity Management in DeFi (UCM-DeFi) – Introduction to Smart Contracts and DeFi (Article 2)
Smart contracts are digital versions of traditional legal agreements programmed to automate the execution of terms and conditions without intermediaries. They are a crucial part of many blockchains and distributed ledger technology applications. However, their immutability can make modifications challenging...Read PDF
Smart contracts are digital versions of traditional legal agreements programmed to automate the execution of terms and conditions without intermediaries. They are a crucial part of many blockchains and distributed ledger technology applications. However, their immutability can make modifications challenging...Read PDF
2023
Blog-28: IT World Canada: Understanding Cybersecurity Management in DeFi (UCM-DeFi) – The Origin of Modern Decentralized Finance (Article 1)
The modern financial system has become more decentralized, moving away from the centralized system used by banks in the past. Decentralized finance (DeFi) eliminates intermediaries from transactions, allowing for two or more users to execute financial transactions without a central authority...Read PDF
The modern financial system has become more decentralized, moving away from the centralized system used by banks in the past. Decentralized finance (DeFi) eliminates intermediaries from transactions, allowing for two or more users to execute financial transactions without a central authority...Read PDF
2023
Blog-27: IT World Canada: Understanding current cybersecurity challenges in law (UCCCL) - Legal Considerations for Artificial Intelligence and Technological Development (Article 6)
With strong competition among countries around the world to become cutting edge leaders in AI, artificial intelligence has been a driving force of innovation in the digital economy. Indeed, Canada has been working to place itself among other global leaders in dynamic AI development, with the Canadian artificial intelligence sector receiving...Read PDF
With strong competition among countries around the world to become cutting edge leaders in AI, artificial intelligence has been a driving force of innovation in the digital economy. Indeed, Canada has been working to place itself among other global leaders in dynamic AI development, with the Canadian artificial intelligence sector receiving...Read PDF
2022
Blog-26: IT World Canada: Understanding current cybersecurity challenges in law: Data Breaches and Increased Data Awareness (Article 5)
Data breaches are incidents in which information is stolen or taken from a system without the knowledge or authorization of the owner of that system. Data breaches can expose confidential, sensitive, or protected information to an unauthorized person or ...Read PDF
Data breaches are incidents in which information is stolen or taken from a system without the knowledge or authorization of the owner of that system. Data breaches can expose confidential, sensitive, or protected information to an unauthorized person or ...Read PDF
2022
Blog-25: IT World Canada: Understanding current cybersecurity challenges in law: balancing responsibilities in digital content censorship (Article 4)
Public broadcasting regulations and legislation have long provided the regulations for information which is shared in the public domain, including newspaper, radio, and television. During the COVID-19 pandemic we saw many of our family, friends, colleagues, and acquaintances...Read PDF
Public broadcasting regulations and legislation have long provided the regulations for information which is shared in the public domain, including newspaper, radio, and television. During the COVID-19 pandemic we saw many of our family, friends, colleagues, and acquaintances...Read PDF
2022
Blog-24: IT World Canada: Understanding current cybersecurity challenges in law: determining online jurisdictional authority (Article 3)
When a crime takes place or a dispute occurs between two parties who reside within the same geographic location, the determination of which law applies to that scenario is easily distinguished as being the law of that geographic location. When a dispute occurs between two parties ...Read PDF
When a crime takes place or a dispute occurs between two parties who reside within the same geographic location, the determination of which law applies to that scenario is easily distinguished as being the law of that geographic location. When a dispute occurs between two parties ...Read PDF
2022
Blog-23: IT World Canada: Understanding current cybersecurity challenges in law: digital governance and social responsibility meet user-generated content (Article 2)
Digital governance refers to the strategic management of a governing body or corporation, over that which is connected to their position and function online – including the impacts of their actions in that position...Read PDF
Digital governance refers to the strategic management of a governing body or corporation, over that which is connected to their position and function online – including the impacts of their actions in that position...Read PDF
2022
Blog-22: IT World Canada: Understanding current cybersecurity challenges in law: data sovereignty & cross-border data transfers (Article 1)
Most of us would likely be unsurprised to learn that the vast majority of our personal and professional data is stored in the cloud. The most popular social media apps – such as Instagram, Twitter, Facebook, and LinkedIn – all use cloud-based data storage for user accounts, profiles, uploaded content, and more...Read PDF
Most of us would likely be unsurprised to learn that the vast majority of our personal and professional data is stored in the cloud. The most popular social media apps – such as Instagram, Twitter, Facebook, and LinkedIn – all use cloud-based data storage for user accounts, profiles, uploaded content, and more...Read PDF
2022
Blog-21: IT World Canada: Understanding cybersecurity management for FinTech: cybersecurity policy and strategy management (Article 6)
Cyber-attacks are on the rise with every passing day, and so is the cost associated with the damage caused by them. To protect the financial institutions from the menace of these cyber-attacks, a cybersecurity policy and strategy sets the standards to: monitor cyber activities on premises,...Read PDF
Cyber-attacks are on the rise with every passing day, and so is the cost associated with the damage caused by them. To protect the financial institutions from the menace of these cyber-attacks, a cybersecurity policy and strategy sets the standards to: monitor cyber activities on premises,...Read PDF
2022
Blog-20:IT World Canada: Understanding cybersecurity management for FinTech: security issues on financial market infrastructures (Article 5)
Financial market infrastructure (FMI) serves as the backbone of financial markets. It allows financial transactions to take place between people, financial institutions, and businesses in a cheaper and more efficient manner. It is the key component between financial institutions that exchange payments,...Read PDF
Financial market infrastructure (FMI) serves as the backbone of financial markets. It allows financial transactions to take place between people, financial institutions, and businesses in a cheaper and more efficient manner. It is the key component between financial institutions that exchange payments,...Read PDF
2022
Blog-19: IT World Canada: Understanding cybersecurity management for FinTech: cybersecurity vulnerabilities and risk in FinTech (Article 4)
FinTech revolves around technologies such as cloud, blockchain, AI, and mobile devices that are used for financial transaction payments, cryptocurrencies, money transfers, trading, and regulatory compliance. With so much monetary value associated with all these technologies,...Read PDF
FinTech revolves around technologies such as cloud, blockchain, AI, and mobile devices that are used for financial transaction payments, cryptocurrencies, money transfers, trading, and regulatory compliance. With so much monetary value associated with all these technologies,...Read PDF
2021
Blog-18: IT World Canada: Understanding cybersecurity management for FinTech: cybersecurity threats in FinTech (Article 3)
With a plethora of digital wallet methods, financial cyber risks such as fraudulent transactions, extortion, denial of service attacks, and credit card fraud have become frequent. These cyber-attacks are capable enough to cause systemic risk to the financial sector...Read PDF
With a plethora of digital wallet methods, financial cyber risks such as fraudulent transactions, extortion, denial of service attacks, and credit card fraud have become frequent. These cyber-attacks are capable enough to cause systemic risk to the financial sector...Read PDF
2021
Blog-17: IT World Canada: Understanding cybersecurity management for FinTech : information security governance in FinTech (Article 2)
Information is the key to success in the contemporary era. Just as there are two sides of a coin, there are two perspectives of a cyber-attack. On one hand, attackers seek information to take advantage of potential flaws in an organization’s architecture, processes, and design; exploiting these flaws to make money...Read PDF
Information is the key to success in the contemporary era. Just as there are two sides of a coin, there are two perspectives of a cyber-attack. On one hand, attackers seek information to take advantage of potential flaws in an organization’s architecture, processes, and design; exploiting these flaws to make money...Read PDF
2021
Blog-16: IT World Canada: Understanding cybersecurity management for FinTech (UCMF) - introduction to FinTech and the importance of security objects (Article 1)
FinTech encompasses a wide array of technological strategies, many of which have either improved the functionality of existing financial products and services or enabled the development of novel technological solutions for the financial sector. With the rapid growth of digital platforms, ...Read PDF
FinTech encompasses a wide array of technological strategies, many of which have either improved the functionality of existing financial products and services or enabled the development of novel technological solutions for the financial sector. With the rapid growth of digital platforms, ...Read PDF
2021
Blog-15: IT World Canada:Understanding Android Malware Families (UAMF) – file infector and potentially unwanted applications (Article 6)
File infector is a malware that attaches itself to APK files, which contain all the data related to an Android application. File infector gets installed with APK files, and it gets executed when the APK file is installed. The APK file can be any Android application such as a game, word processing file, ...Read PDF
File infector is a malware that attaches itself to APK files, which contain all the data related to an Android application. File infector gets installed with APK files, and it gets executed when the APK file is installed. The APK file can be any Android application such as a game, word processing file, ...Read PDF
2021
Blog-14: IT World Canada:Understanding Android Malware Families (UAMF) – Adware and Backdoor (Article 5)
Mobile adware refers to the advertising material hidden inside legitimate apps infected by malware. Most of these apps are available from third-party sources. Adware continuously shows unwanted advertisements on mobile screens even if the user attempts to force-close the app...Read PDF
Mobile adware refers to the advertising material hidden inside legitimate apps infected by malware. Most of these apps are available from third-party sources. Adware continuously shows unwanted advertisements on mobile screens even if the user attempts to force-close the app...Read PDF
2021
Blog-13: IT World Canada:Understanding Android Malware Families (UAMF) – Riskware – is it worth it? (Article 4)
Riskware is defined as a legitimate program that presents potential risks to the security vulnerabilities on a device. Although it is a legitimate program, bad actors use Riskware to steal information from the device and redirect users to malicious websites or perform functions at the expense of device security...Read PDF
Riskware is defined as a legitimate program that presents potential risks to the security vulnerabilities on a device. Although it is a legitimate program, bad actors use Riskware to steal information from the device and redirect users to malicious websites or perform functions at the expense of device security...Read PDF
2021
Blog-12: IT World Canada:Understanding Canadian Cybersecurity Laws: refactored — our series in summary (Article 10)
In this tenth and final article in our Understanding Canadian Cybersecurity Laws series, we will look back through the previous nine articles and revisit the topics covered in each of them. Our journey begins with the first article, The Foundations, first published by IT World Canada on January 13, 2020... Read PDF
In this tenth and final article in our Understanding Canadian Cybersecurity Laws series, we will look back through the previous nine articles and revisit the topics covered in each of them. Our journey begins with the first article, The Foundations, first published by IT World Canada on January 13, 2020... Read PDF
2021
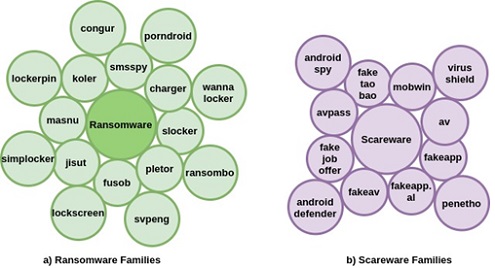
Blog-11: IT World Canada:Understanding Android Malware Families (UAMF) – Ransomware and scareware (Article 3)
Ransomware is malicious software used by individuals to encrypt documents on computers or digital devices. Perpetrators demand a ransom from the owner of a device to access the victim’s documents; once in, criminals install ransomware on their mobile phone or computer... Read PDF
Ransomware is malicious software used by individuals to encrypt documents on computers or digital devices. Perpetrators demand a ransom from the owner of a device to access the victim’s documents; once in, criminals install ransomware on their mobile phone or computer... Read PDF
2021
Blog-10: IT World Canada:Understanding Canadian Cybersecurity Laws: Legislative Modernization — Responding and Adapting to Technological Change in a Global Domain (Article 9)
In this article, we will discuss the Digital Charter Implementation Act, 2020, which was tabled by the government on November 17, 2020, along with its progeny: the Consumer Privacy Protection Act (CPPA) and the Personal Information and Data Tribunal Act... Read PDF
In this article, we will discuss the Digital Charter Implementation Act, 2020, which was tabled by the government on November 17, 2020, along with its progeny: the Consumer Privacy Protection Act (CPPA) and the Personal Information and Data Tribunal Act... Read PDF
2021
Blog-09: IT World Canada:Understanding Android Malware Families (UAMF) – The Trojan: An impersonator in the background (Article 2)
The trojan is a sneaky impersonator that behaves like a legitimate program. It can hide in the background and steal information from the device. Trojan samples often delete, modify, block, and copy data to disrupt services provided by the operating system... Read PDF
The trojan is a sneaky impersonator that behaves like a legitimate program. It can hide in the background and steal information from the device. Trojan samples often delete, modify, block, and copy data to disrupt services provided by the operating system... Read PDF
2021
Blog-08: IT World Canada:Understanding Android Malware Families (UAMF) – The Foundations (Article 1)
Android malware is one of the most serious threats on the internet and has witnessed an unprecedented upsurge in recent years. There is a need to share the fundamental understanding of behaviour... Read PDF
Android malware is one of the most serious threats on the internet and has witnessed an unprecedented upsurge in recent years. There is a need to share the fundamental understanding of behaviour... Read PDF
2021
Blog-07: IT World Canada:Understanding Canadian Cybersecurity Laws: Measuring Up — Outlining Existing National Cybersecurity Legislation in Canada, the UK, Australia, and the US (Article 8)
In this article, we will outline the relevant national privacy and cybersecurity-related laws currently in effect in the United Kingdom, Australia, and the United States, as fellow common law countries... Read PDF
In this article, we will outline the relevant national privacy and cybersecurity-related laws currently in effect in the United Kingdom, Australia, and the United States, as fellow common law countries... Read PDF
2020
Blog-07: IT World Canada:Understanding Canadian cybersecurity laws: Deep, dark, and undetectable – Canadian jurisdictional considerations in global encrypted networks (Article 7)
The rapid growth of encryption technology has revolutionized the online marketplace and helped to enable the creation of anonymous online networks, like the Dark Net ... Read PDF
The rapid growth of encryption technology has revolutionized the online marketplace and helped to enable the creation of anonymous online networks, like the Dark Net ... Read PDF
2020
Blog-06: IT World Canada:Understanding Canadian cybersecurity laws: Peer-to-peer privacy protection - “Intrusion upon seclusion” and the protection of intimate images (Article 6)
The prevalence of digital communication has created nearly limitless possibilities for the rapid, large-scale sharing of private communications, intimate images, and personal information... Read PDF
The prevalence of digital communication has created nearly limitless possibilities for the rapid, large-scale sharing of private communications, intimate images, and personal information... Read PDF
2020
Blog-05: IT World Canada:Understanding Canadian Cybersecurity Laws: Insert Something Clever Here - Canada’s Anti-Spam Legislation (Article 5)
As we continue to adapt to the changing demands to navigate the spread of COVID-19, an increasing number of workspaces and social interactions have had to rely much more heavily on email and ... Read PDF
As we continue to adapt to the changing demands to navigate the spread of COVID-19, an increasing number of workspaces and social interactions have had to rely much more heavily on email and ... Read PDF
2020
Blog-04: IT World Canada:Understanding Canadian Cybersecurity Laws: Interpersonal Privacy and Cybercrime - Criminal Code of Canada (Article 4)
The global spread of COVID-19 has been a huge catalyst in our increased reliance on digital technologies, particularly our networked communication infrastructure. With the rapid influx of demand for ... Read PDF
The global spread of COVID-19 has been a huge catalyst in our increased reliance on digital technologies, particularly our networked communication infrastructure. With the rapid influx of demand for ... Read PDF
2020
Blog-03: IT World Canada:Understanding Canadian cybersecurity laws: Privacy Protection in the Modern Marketplace-PIPEDA (Article 3)
With the global spread of COVID-19, on-line scams are circulating and malicious actors have been spreading malware intended to steal individual information through both personal and corporate networks. We previously outlined... Read PDF
With the global spread of COVID-19, on-line scams are circulating and malicious actors have been spreading malware intended to steal individual information through both personal and corporate networks. We previously outlined... Read PDF
2020
Blog-02: IT World Canada:Understanding Canadian cybersecurity laws: Privacy and access to information, the Acts (Article 2)
The Privacy Act and the Access to Information Act were both implemented by the Canadian federal government in 1985 and have acted as a starting point for more recent legislation... Read PDF
The Privacy Act and the Access to Information Act were both implemented by the Canadian federal government in 1985 and have acted as a starting point for more recent legislation... Read PDF
2020
Blog-01: IT World Canada:Understanding Canadian cybersecurity laws: the foundations (Article 1)
The end of 2019 marked the end of a decade that has been shaped by rapid technological development, advancing data-use research, and an increasingly hyper-connective global infrastructure... Read PDF
The end of 2019 marked the end of a decade that has been shaped by rapid technological development, advancing data-use research, and an increasingly hyper-connective global infrastructure... Read PDF
2020










.jpg)
-01.jpg)
.jpg)